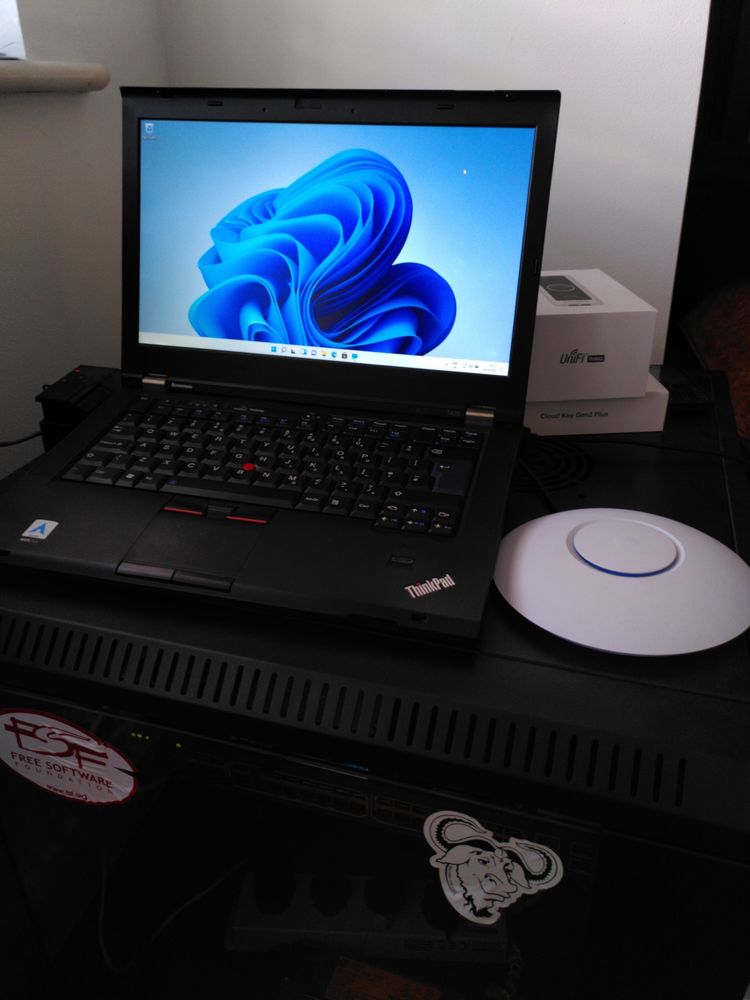
In this post I will be learning about Intune deployment. I have pre-deployed a fresh Windows 11 test device onto my Hybrid Active Directory domain (Azure AD is synced with On-Prem Domain Controller), in this post I will do a basic intune setup, and then enroll the device into intune, and apply a basic policy.
This guide assumes you have the following:
- A Hybrid Azure AD domain
- Office 365/Azure AD accounts with the relevant Office licenses (I am using a Enterprise Mobility + Security E5 trial license).
- A Windows 11 device joined to your domain and logged into a domain account linked with the license mentioned above.
1. Install Company Portal and enroll the device
To install company portal, you must login to Microsoft Business Store in a browser, search for “Company Portal” and install it onto your device as shown below

When company portal has installed, open the start menu, open Company Portal, sign in, and enroll your device onto intune as shown:
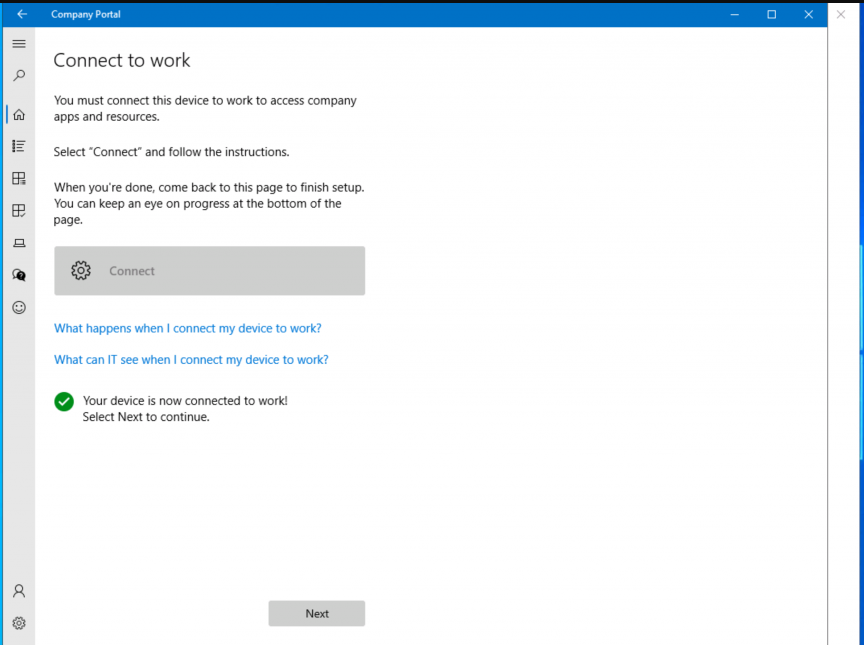
The device is now successfully connected to Intune. You can automate this process through Active Directory, however, since I am using a trial license for learning, I do not want to enroll all of my domains computers into Intune, so I did the above manual process.
2. Check out the endpoint manager
Start by logging into endpoint.microsoft.com, and clicking devices:
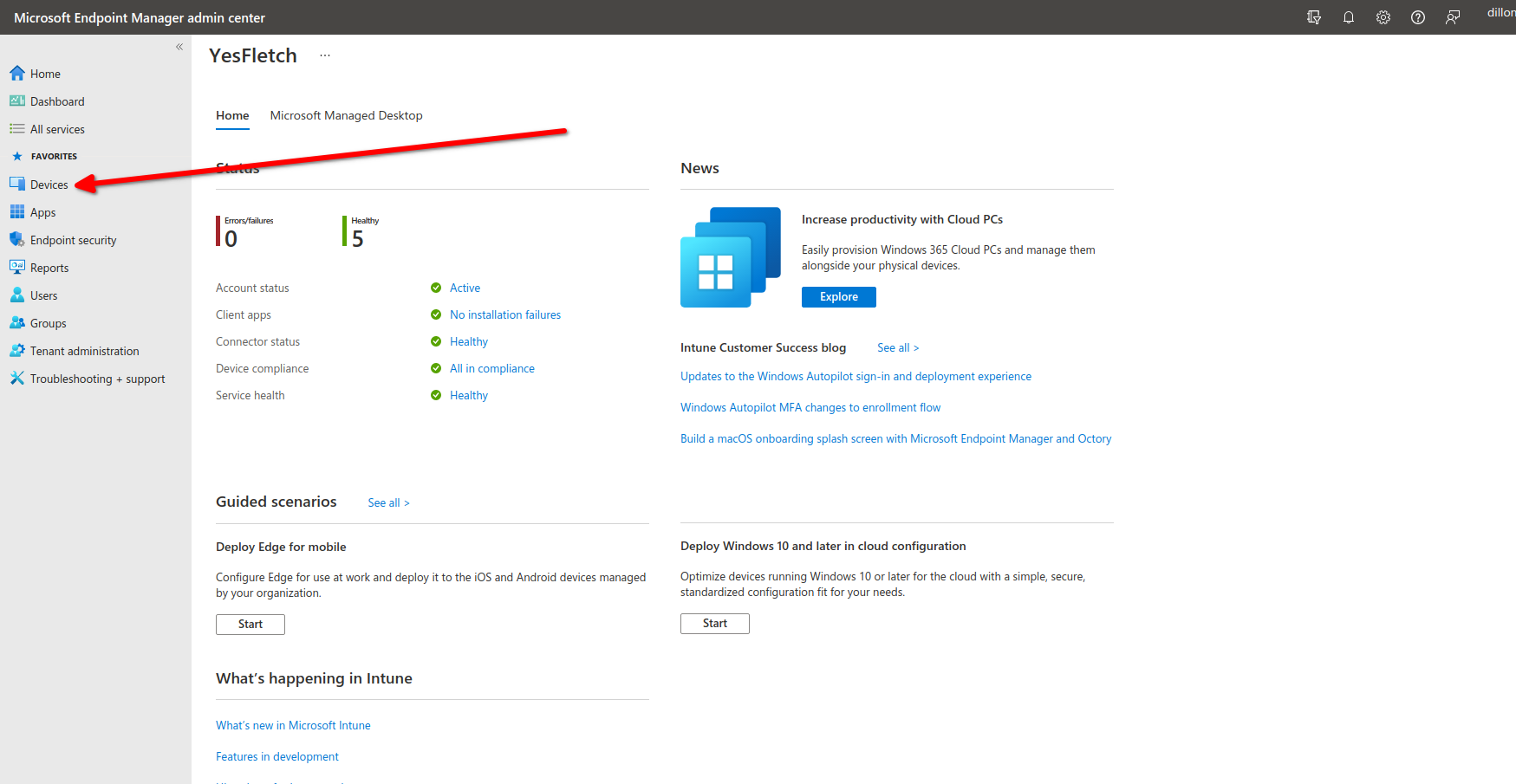
Clicking this will bring up all devices enrolled into intune:
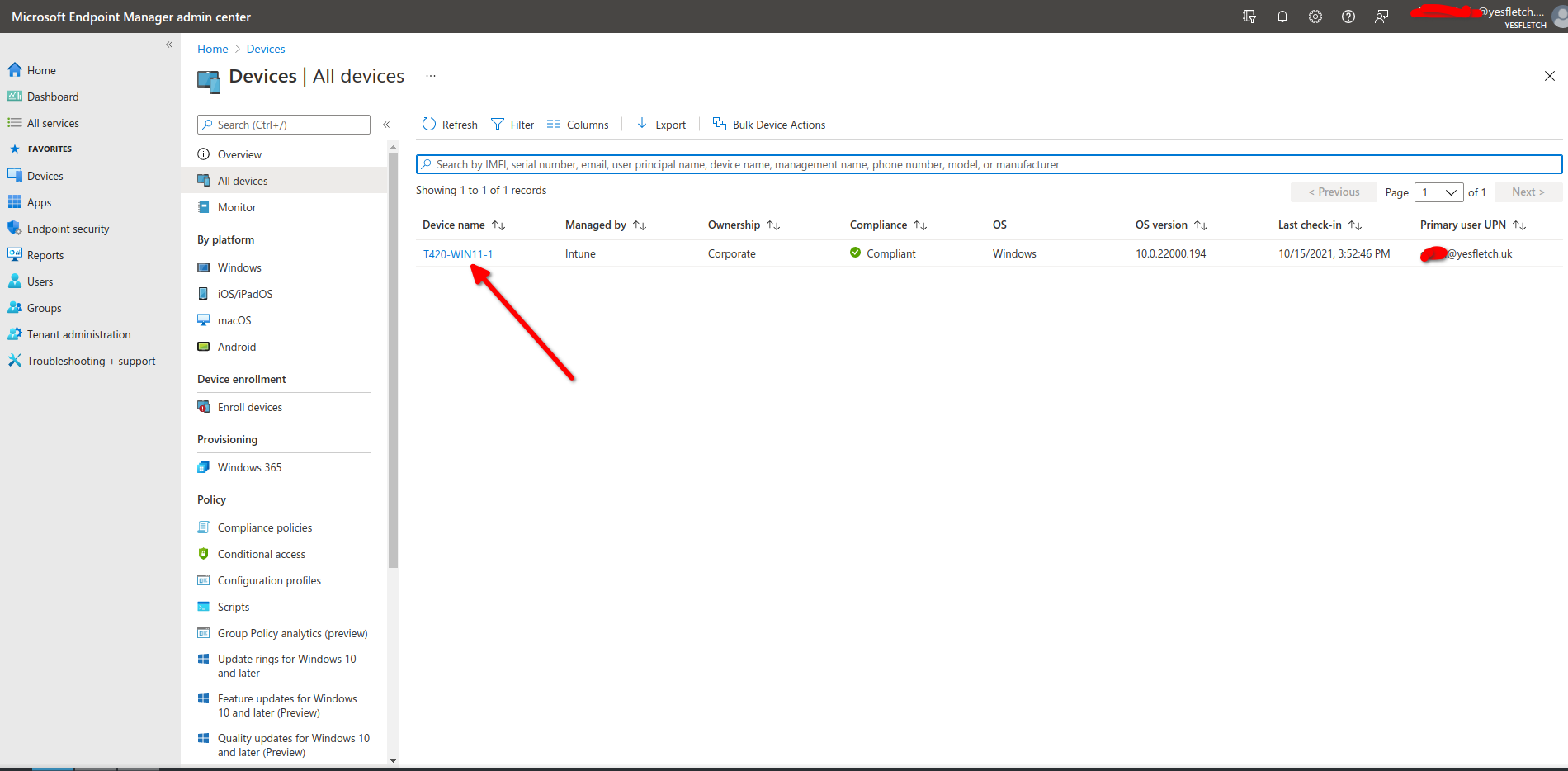
The device is now listed in endpoint manger, this means enrollment definetly was successful! Now, click on the device name:
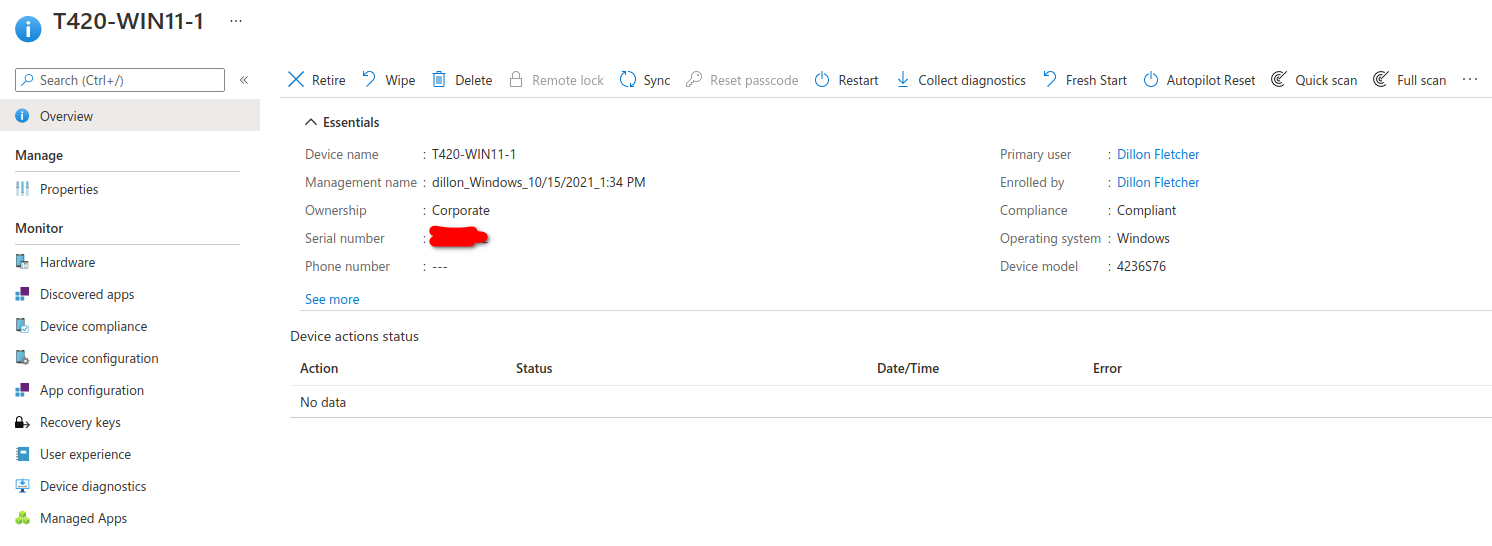
This will show device specific options, you can retire, wipe, reboot, Autopilot Reset (reverts device to an OOBE domain joined state), Fresh start (removes all extra Win32 applications), and anti virus scan. On the menu on the left, you can also find device information, such as compliance info, apps installed on the machine, diagnostics, and bitlocker recovery keys.
3. Setup a BitLocker encryption policy
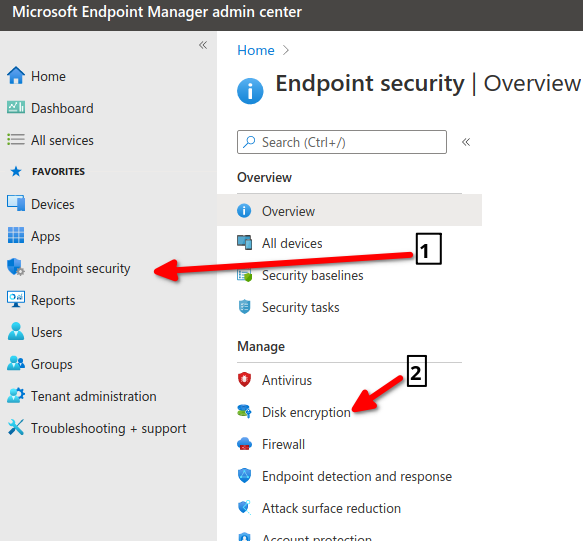
Go back to the home screen and click Endpoint Security, then click Disk Encryption:
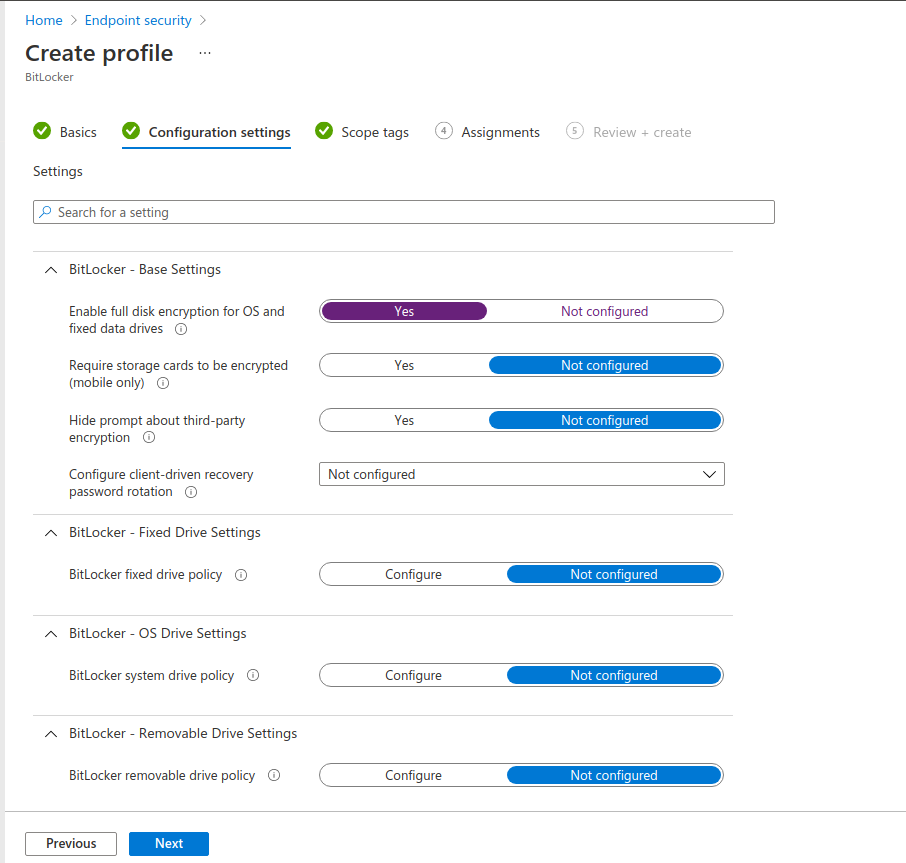
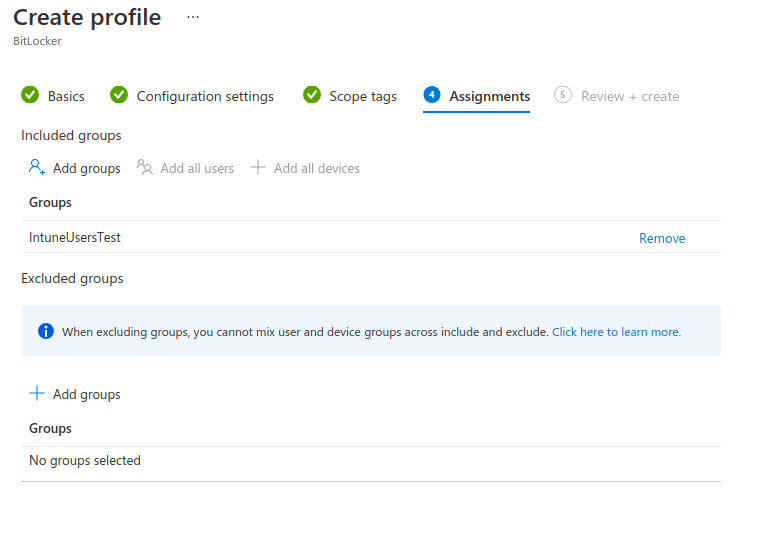
Create a new profile with the following settings:
Now your device should be enrolled into Bitlocker. You can check that all your devices would be compliant by adding a compliance policy. It is a similar process and can be found under “Devices > Compliance Policies”. This is what will trigger the “Compliant” or “Error” under the devices compliant status.
Now sync the device from endpoint device options, and ensure that it begins encrypting:
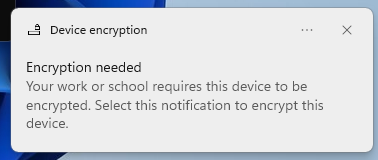
I received this notification on the Thinkpad, meaning that the policy was successfully pushed. I assume this process would normally start automatically, but since my test machine is so old, it doesnt have a TPM chip to store encryption keys on, and clicking the notification prompted me to turn on the TPM in the BIOS. However, it is a good proof of concept I have successfully learnt the basics of Intune! From here, I can learn to push apps/app policies and configuration policies.
No comment yet, add your voice below!